SingHealth and the Agency for Science, Technology and Research (A*STAR), with support from the Integrated Health Information Systems (IHiS), have co-developed a chatbot known as “Doctor Covid” to improve care for COVID-19 patients at community care facilities.
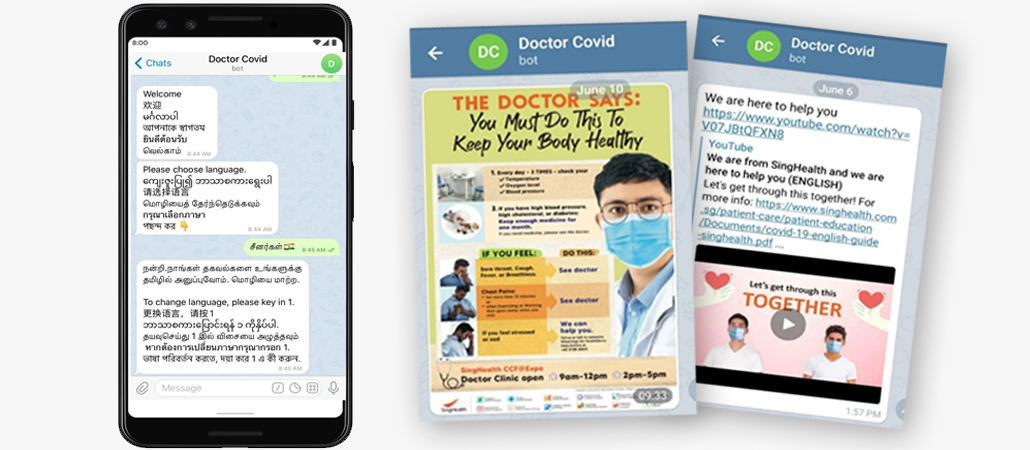
The mobile app, Doctor Covid, boasts a variety of features in the patients’ native languages to help with effective communication and to support the medical teams in close monitoring of their health and well-being.
Community care facilities support COVID-19 patients who are clinically well and no longer require acute care, as well as new cases with mild symptoms that do not need hospital care, the current majority being migrant workers presently.
It is a challenging task to provide personalised care to large groups of residents at recovery facilities and this is complicated further by the language barriers between medical teams and migrant workers.
Multi-lingual platform to help effective communication with migrant workers
Doctor Covid features up to seven different languages that migrant workers can subscribe to – English, Mandarin, Malay, Tamil, Bengali, Thai and Burmese.
As migrant workers interact with the chatbot in the languages they are familiar with, it helps keep them engaged and ensures that they receive and understand the content that is communicated to them.
It also ensures greater accuracy in the information they submit via the chatbot, such as responses to questions about their well-being.
“The experience of being diagnosed with COVID-19 can be a stressful one, especially for migrant workers who are uncertain as to what to expect and may face language barrier issues with the healthcare workers caring for them. At the same time, it is no easy feat for medical teams to take care of large groups of residents in community care facilities. Doctor Covid leverages innovation and technology to better reach out, engage and care for these residents, while allowing healthcare professionals to gain better insight into how each resident is doing in their recovery,” said Franklin Tan, Director, Office for Service Transformation, SingHealth.
“We will also be deepening the sophistication of the platform by incorporating AI mechanisms into Doctor Covid and establishing a stronger two-way interaction with residents, while at the same time be able to utilise the data collected for research purposes.”
Doctor Covid issues important notifications and reminders
Doctor Covid disseminates critical information including medical, nursing, and operational announcements, as well as reminders to submit vital signs inputs such as daily temperature and blood pressure readings.
These are communicated on a daily basis to ensure that the workers are kept abreast of the situation and understand their recovery journey.
Clinical and psychosocial surveillance
Migrant workers use Doctor Covid to respond to questions that assess their clinical risk factors and mental well-being. This is done through easy-to-understand questionnaires with audio capabilities.
The data is then sent to SingHealth’s patient experience teams who ensure timely intervention where required. The data collected will also facilitate further AI-driven diseases triaging, progression and clinical outcome prediction.
“We are pleased that our capabilities in system architectural design, software engineering, and data science were able to support SingHealth in its sterling efforts to provide quality care to recovering workers at the community care facilities.”
“Through close collaboration, A*STAR and SingHealth were able to harness digital tools and artificial intelligence to develop this tool to facilitate better communication and engagement with the recovering workers, as well as generate data insight for the medical teams,” said Dr Rick Goh, Department Director, Computing & Intelligence, Institute of High Performance Computing (IHPC), A*STAR.
Doctor Covid helps minimise the risk of viral transmissions. With communication and monitoring of residents taking place virtually, medical teams reduce prolonged face-to-face contact with COVID-19 patients and the time spent in the “red zone” of the care facilities, while ensuring that comprehensive care is continued.
Conversational AI chatbot to be integrated in next phase
Using artificial intelligence (AI) such as machine learning, natural language processing and optical character recognition, Doctor Covid will be able to capture, analyse and respond to complex COVID-19-related questions posed by migrant workers in their respective native languages. This will be launched later this year.
Moving forward, data from Doctor Covid may be integrated with other COVID-19 data platforms and registries to form a big data platform with AI analytical tools for operational and research purposes.
The data collected by Doctor Covid, which is anonymised to ensure data privacy, can also be used to identify trends, risk indicators, clinical outcomes, as well as evidence-based practices as a study into the COVID-19 pandemic and care of migrant workers, as well as to prepare for future infectious disease health emergencies.
















