With cyber threats are ever on the rise, everyone has been warned to adopt good cyber hygiene practices. But what exactly are they and which are best? Even if you do know them, do they fit your organisation’s needs and present concerns?
Not to worry, the Australian Cyber Security Centre (ACSC) has got you covered.
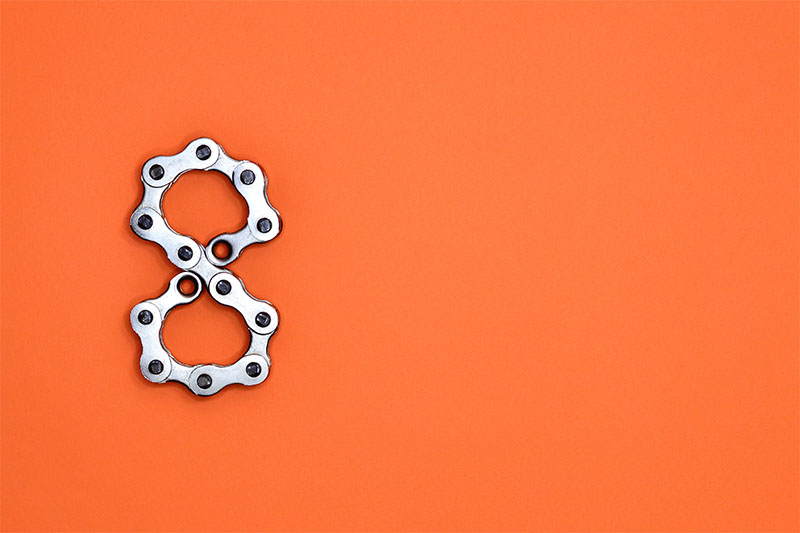
They have released a list of eight essential mitigation strategies to protect an organisation’s systems from a range of cyber threats. Known as the Essential Eight, none are to be deleted since no single mitigation strategy can fully guarantee a cyber security incident being deflected. The eight strategies should form the baseline to make it harder for adversaries to compromise systems.
ACSC says implementing the Essential Eight proactively can be more cost-effective in terms of time, money and effort than having to respond to a successful large-scale cyber security incident.
Taking the Steps to Security
Before the Essential Eight are undertaken, ACSC recommends some preparation beforehand.
First, organisations should identify which systems require protection. This could be systems which store, process or communicate sensitive information or other information with a high availability requirement.
Mapping adversaries who are likely to target their systems, such as cyber criminals, nation-states or malicious insiders, should also be identified.
Third, determining a level of protection required is necessarily. Organisations may select mitigation strategies to implement based on the risks to business activities from specific cyber threats.
An implementation order for each cyber threat is suggested. This will assist organisation in building a strong cyber security posture for their systems, says ACSC. Once desired mitigation strategies have been implemented to an initial level, focus should be then spent on increasing the maturity of their implementation so that the full alignment with the intent of each mitigation strategy is eventually reached.
The Essential Eight
The Essential Eight are categorise into three segments.
Mitigation strategies to prevent malware delivery and execution are the first. Within this category are application whitelisting, patch applications, configure Microsoft Office macro settings, and user application hardening.
Application whitelisting of approved or trusted programs is need so that all non-approved applications are prevented from executing. Patching applications prevents security vulnerabilities which may execute malicious code on systems. The configuration of macro settings blocks macros from the Internet, allowing only vetted macros, thus preventing malware. Additionally, through user application hardening, web browsers can be configured to block Flash, ads and Java on the internet.
Second, are mitigation strategies to limit the extent of cyber security incidents. This category makes three suggestions. The first, restrict administrative privileges to deny the ‘keys to the kingdom’ and thus the stealing of information and systems. Next, operating systems must be patched to prevent further compromise of the system. Additionally, multi-factor authentication for VPNs, RDP, SSH and other remote access, should be used to make it harder for adversaries to access sensitive information and systems.
Finally, daily backups is the last of the third segment of mitigation strategies to recover data and system availability. Daily backups of important or new changed data, software and configuration settings, stored disconnected, retained, should be done for at least three months. Restoration should be tested initially, annually and when IT infrastructure changes.
In doing so, information can be accessed again should a cyber security incident happen.
For a full report and further information of the Essential Eight, click here.
















