The Office of the Australian Information Commissioner (OAIC) and the CSIRO’s (Commonwealth Scientific and Industrial Research Organisation) Data61 have released a guide, called ‘The De-Identification Decision-Making Framework (DDF)’, to assist organisations to de-identify their data effectively.
The framework is meant to be a practical and accessible guide for Australian organisations that handle personal information and are considering sharing or releasing it to meet their ethical responsibilities and legal obligations, such as those under the Privacy Act 1988.
The guide is adapted from the UK resource, The Anonymisation Decision-Making Framework, and it is the result of a close collaboration between CSIRO and OAIC, with input from the Australian Bureau of Statistics (ABS) and the Australian Institute for Health and Welfare (AIHW).
The framework can help data custodians to identify and address the key factors relevant to their particular data sharing or release situation, including privacy risk analysis and control, stakeholder engagement, and impact management. The DDF focuses on assessing and managing re-identification risks within the context of the data release or share. It encourages organisations to think more broadly and consider the data release environment, as well as the techniques and controls applied to the data.
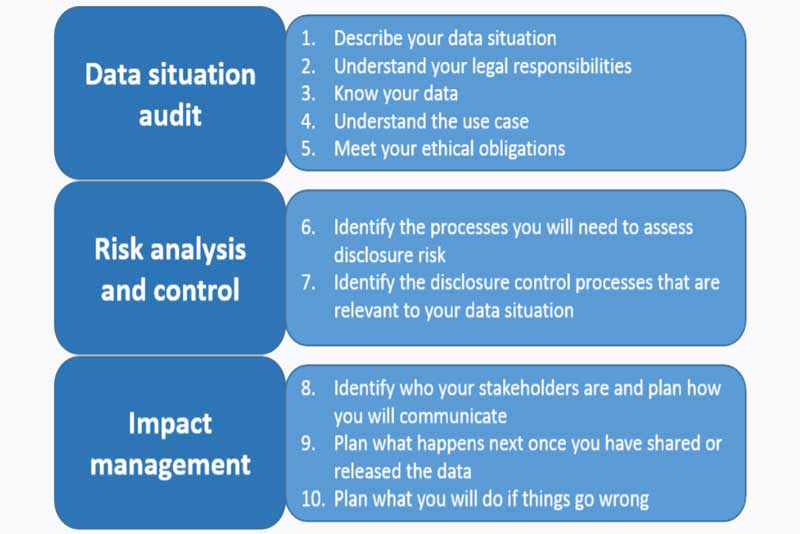
The DDF is made up of ten components:
- Describe your data situation
- Understand your legal responsibilities
- Know your data
- Understand the use case
- Meet your ethical obligations
- Identify the processes you will need to assess disclosure risk
- Identify the disclosure control processes that are relevant to your data situation
- Identify who your stakeholders are and plan how you will communicate
- Plan what happens next once you have shared or released the data
- Plan what you will do if things go wrong
Presentation of the DDF components as a numbered list is not intended to suggest that this is the right order to do them. For example, stakeholder engagement plays an important role in shaping purpose of the data access arrangements, costs, breach policies, outputs and public messaging.
The ten components of the DDF are grouped into three core de-identification activities:
A data situation audit (Components 1-5): This activity will help identify and frame those issues relevant to the data situation. The organisations will encapsulate and systematically describe the data, what theyare trying to do with it and the issues thereby raised. A well-conducted data situation audit is the basis for the next core activity.
Risk analysis and control (Components 6-7): Here the technical processes are considered that will have to be used in order to both assess and manage the disclosure risk associated with the data situation.
Impact management (Components 8-10): Here the measures are considered that should be in place before data is released or share to help communicate with key stakeholders, ensure that the risk associated with data remains negligible going forward, and work out what the organisation should do in the event of an unintended disclosure or security breach.
The report cautions that de-identification is not an exact science and, even using the DDF, it requires complex judgement calls. The DDF is intended to help data custodians make sound decisions based on best practice, but it is not a step-by-step algorithm or a linear checklist. It recommends that users seek expert advice on the de-identification process, particularly with the more technical risk analysis and control activities.
Timothy Pilgrim, Australian Information and Privacy Commissioner, commented, “De-identification is one solution for sharing and releasing data while meeting legislative demands and community expectations. It is an exercise in risk management, rather than an exact science, and it’s important that we strike the right balance between maintaining useful data and making sure it’s safe.”
“Deciding whether data should be released or shared – and if so, in what form – requires careful consideration. A range of factors needs to be considered, from ethical and legal obligations to technical data questions. Integrating the different perspectives on the topic of de-identification into a single, comprehensible framework is what this guide is all about,” he added.
Dr. Christine O’Keefe, the lead author of the guide and Research Scientist at Data61 explained, “At CSIRO’s Data61 we are a trusted advisor to government and industry organisations and we help them access the power of their data by applying deep science, engineering and design to derive insights from it and make it accessible to others without compromising privacy. At present, there is no publicly available, comprehensive risk management guide in Australia to assist organisations with de-identification. That’s why we have set out to create this standalone guide as an adaptation of the existing UK version, the Anonymisation Decision-Making Framework — and make it freely available.
















