The University of Sydney
announced that its researchers developed a comorbidity network for Type 2
diabetes using advanced data mining and network analysis techniques. The new
study was published
in the International Journal of
Medical Informatics.
Researchers from the University of Sydney believe untapped
medical records could be used to predict when a person is at risk of developing
type 2 diabetes.
According to lead author of the study Mr Arif Khan, postdoctoral
researcher from the Centre
for Complex Systems in the Faculty of Engineering and Information
Technologies, it is well known that chronic diseases such as type 2
diabetes do not occur in isolation, and have a shared set of causes common to
many other diseases and disorders.
“Chronic diseases like type 2 diabetes progress slowly and,
in many cases, patients are unaware of their condition. When they are admitted
in to hospital for any incidence, type 2 diabetes often comes up as secondary
diagnosis. This makes the overall treatment plan more complex, increasing
‘Length of Stay’ in hospital and cost,” Mr Khan added.
As such, the aim of the research is to understand how health
trajectory differs between type 2 diabetes and non-type 2 diabetes patients
with the help of comorbidity network.
Together with Capital
Markets Cooperative Research Centre (CMCRC), the researchers analysed 1.4
million admission records from nearly 1 million de-identified patients using
routinely collected administrative healthcare data. The dataset used for this
study was provided by data custodians Capital Markets CRC Ltd. and HAMBS Ltd.
The dataset was then filtered and sampled to obtain a cohort
of 2300 diabetics and 2300 non-diabetic patients.
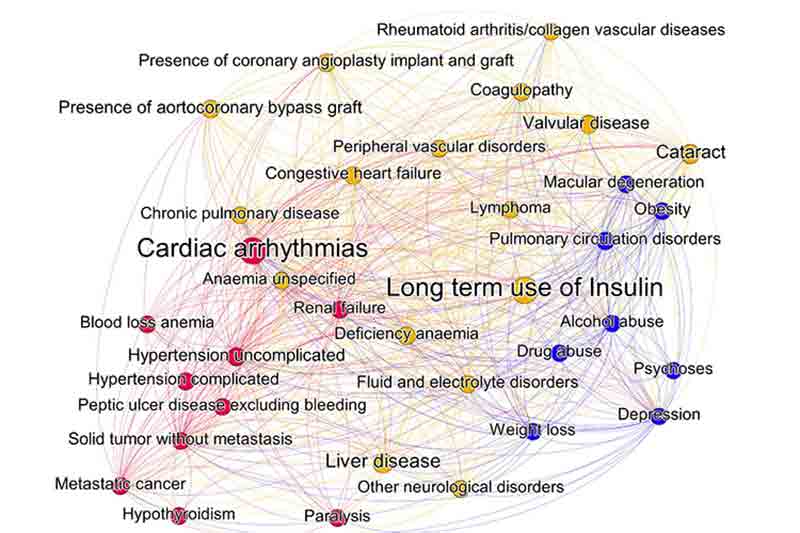
Using advanced data mining and network analysis techniques,
the researchers evaluated the health of the cohort and developed a comorbidity
network – a way of visualising the health journey of the type 2 diabetes
patients.
The network models the relative prevalence of type 2
diabetes comorbidities, meaning additional diseases or disorders co-occurring
with a primary disease and their transition patterns, thereby representing the
progression of the disease.
In the network image, the size of the nodes (circles) and
labels are proportional to the prevalence of corresponding health conditions.
Nodes marked in the same colour belong to same clusters of related health
conditions. Arcs, in clockwise direction, indicate transition from one health
condition to another.
The researchers found that, over time, prevalence of
comorbidities in the group of diabetic patients was almost double that of the
non-diabetic patients over time, indicating entirely different ways of disease
progression.
Study co-author Dr Shahadat Uddin from the Centre for
Complex Systems and the Charles Perkins Centre
said the comorbidity network could help healthcare providers proactively
identify patients at higher risk of developing chronic disease.
“By using existing administrative healthcare data – which
are routinely collected but often neglected in health research – we have been
able to understand the ‘disease footprints’ left by chronic patients,” Dr Uddin
said.
“These insights can subsequently help healthcare providers
to better understand high-risk diseases and to formulate appropriate preventive
health policies,” added study co-author Dr Uma Srinivasan from
the CMCRC.
The researchers predicted their comorbidity
network could also be used effectively to monitor other chronic diseases, such
as cardiovascular diseases.
















