Worldwide, 2019 saw waves of cyberattacks that amounted to trillions of dollars in losses. Hackers are constantly devising way new ways to break through these constructed walls of security. Hence, it is crucial now more than ever to be vigilant and prepared for such attacks.
Both the public and private sectors strive to ensure that digital security efforts remain robust in an ever-changing landscape. As with other countries, Finland has set in place strategies to combat cyber resilience challenges and protect its businesses’ and citizens’ data.
OpenGov had the opportunity to speak with Antti Savolainen, Chief Information Security Officer (CISO) for the Ministry for Foreign Affairs of Finland, to gain insights into the measures taken by the Finnish Government to strengthen its cyber resilience.

Savolainen is responsible for the cybersecurity of Finnish foreign and diplomatic service. He plays an important role as a link between business leaders and IT, and his main focus areas are risk management, security awareness and incident management.
Savolainen has CISSP and RIMAP certifications. He is also a host of a track in Disobey-hacker conference.
Savolainen is interested in gamification and cybersecurity of smart cities and peace mediation.
Before joining the MFA in 2005, Savolainen was a security consultant at an IT service provider and an infantry officer in the Finnish Defence Forces.
He is a speaker at the upcoming Singapore OpenGov Leadership Forum 2020 (SG OGLF 2020) and will be sharing his experiences and knowledge in this field.
Finnish government’s approach to cybersecurity
Savolainen shared that the Government of Finland had adopted a resolution on the Nation’s Cyber Security Strategy during its plenary session on 3rd October 2019.
The Finnish Cyber Security Strategy 2019 is focused on key national objectives which are to develop the cyber environment and to safeguard key functions. The reform and implementation of this strategy are based on the political agenda of the present Government.
The current strategy relies on the general principles of the former cybersecurity strategy, laid out by the government in 2013. The present strategy and its implementation are also a part of the implementation of the European Union´s Cyber Security Strategy. Influential changes in the operating environment and the identified development needs for work at the national level have pushed the government to update the national strategy.
Risk management
Savolainen listed the following strategic guidelines of the Finnish Cyber Security Strategy 2019:
- International cooperation
- Improved coordination of cybersecurity management, planning and preparedness
- Developing cybersecurity competence
The cybersecurity development programme is set to go beyond government terms, upgrading the allocation of resources and improvement of cooperation for cybersecurity. National cybersecurity policies will be strengthened and there will be a better understanding of cybersecurity projects, research and development programmes.
As part of the programme, there will be an establishment of a dedicated position of Cyber Security Director by the Ministry of Transport and Communications, for coordinating the national development of cybersecurity.
Technologies for enforcing cyber resilience
There is a wide range of technologies in place to enforce cyber resilience. Savolainen shared that the first step to doing so is cyber hygiene. This refers to all systems and networks being designed to resist different forms of cyber disruptions.
Security culture as the solid base for the security technology
“Naturally the technology is not the single silver bullet in solving the challenges. The resilience to cyberattacks comes with security culture, where awareness and education of it produces a positive end-user experience.”
Antti Savolainen
The ‘system resilience by security culture’ is only possible if the system design, development, testing and implementation are made with discipline manners, for example, the DevSecOps-concept.
But this could also be jeopardised with a false sense of security. The weak usage and monitoring of encryption material (certifications, encryption keys, encryption parameters etc.) is one such example.
A “lazy admin”, system administrators with a lack of self-discipline are the quickest option for attackers to access key assets of the system. Following this, the attacker “lives of the land” and uses the system administration tools, technics and credentials to gain the foothold and broaden the attack.
Savolainen shared on some measures taken for ensuring that cyber resilience is enforced:
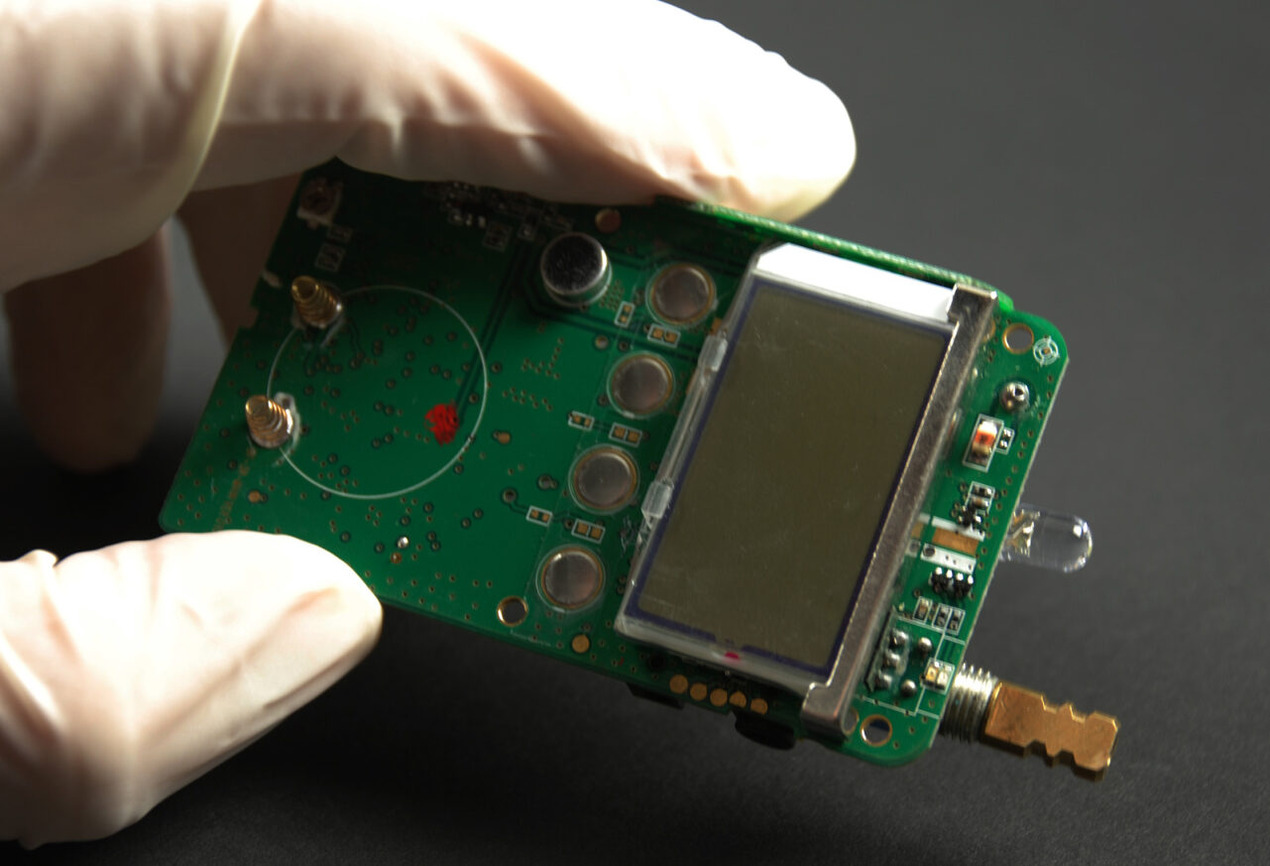
HAVARO
The National Cyber Security Center (NCSC-FI) delivers and maintains a sensor network called HAVARO. It monitors the internet data flow of key organisations of national cyber assets. This includes governmental organisations and companies tied to the national supply (finance, energy, logistics, digitalisation).
The NCSC-FI monitors and notifies the owner of the network from which the alerts originate. This service is an addition to the organisations’ own responsibility for monitoring its networks.
Separated Systems
Isolating the classified information into separated networks and systems ensures that the attack surface is minimalised and beyond the reach from the internet. Savolainen emphasised that this should be made with a strong encryption of the networks (VPN), strong authentication, tempest shielding and constant monitoring and response.
Approaching a cyberattack
Forensics/technical approach
The first notice of the attack comes either from the target, internet operator, NCSA-FI or exchange of international cyber intelligence. It may come also from an independent source, such as the media, a hacker or a security researcher.
After the initial analysis of the attack, some of these measures will be adopted for countering the attack:
- Allow the attack to continue
Note: this is strongly advised only if the cyber/intelligence authorities need more information about the attacker for attribution etc.
- Limit or stop the attack net flow
- Isolation of the compromised part of the network
Further analysis of the attack will be done to recognise the following:
- The attack method in different phases of attack
- Vulnerabilities exploited in the attack
- Origin or waypoints of the attack
- Ultimate target of the attack, more complete list of the compromised assets
- The attacker command & control methods in/out the target, the exfiltration method and address
Initiatives by government for educating people/businesses on cyber resilience
The NCSC-FI releases a monthly Cyber Weather report named Kybersää. This report covers the six information security phenomena as follows:
- Network performance
- Spying
- Malware and vulnerabilities
- Data breaches and leaks
- Scams and phishing
- IoT and automation.
There are three stages for monitoring cybersecurity phenomena. The Cyber Weather conditions may either be calm, worrying or serious.
Anticipating and approaching cyber-attacks
Cyber-attacks are cheaper and easier to launch. Attributing the attack to the source is quite hard, if not impossible. The lack of international regulation provides safe havens for cybercriminals and rogue nations to see this situation as useful for their cyber operations. “The attacks are here to stay,” said Savolainen.
Any regular organisation should agree that they are not capable to avoid the attack in advance, but they should develop the skills to recognise and limit the attack before the attacker gets to the crown jewels.
They should follow the three-step method of surveillance, research and exercise.
Countering a cyberattack
It is imperative for organisations to recognise the attack to stop it. They need to study and research the attacks and exchange information with allies to stay up to the game.
Surveillance and monitoring are important to recognise what should be studied. At the national level, this means getting onboard the internet operators, together with other significant ICT-service and capacity providers. Below the national level, every organisation should take care of their own network, systems and services. Co-operation between the cyber professionals in the same business area amplifies this, especially when business competitors form alliances against cybercriminals.
In Finland, every insurance company reports their cases into a shared information system to counter the insurance frauds. An insurance company can notice if someone claims compensation for the same incident from six different insurance companies.
This same idea about a coalition between competitors could apply in cybersecurity too. They could use proxies, where one does not want to share their findings by their own name. A local security company could do that too.
Ministry for Foreign Affairs of Finland shares a lot of cyber-related information via proxies like NCSC-FI and cybersecurity provider. Mostly the only need is to sanitise the origin of the information to hide our true surveillance capability.
Savolainen stressed that one cannot perform well in real situations without practising and exercising. Or you can avoid common mistakes and make shortcuts when you know the accurate process and contacts.
Exercising should be practised at the team, organisation and national levels. The exercises do not have to be massive and showy to get into the point. Like fire drills, you need to walk the exit route and make sure everyone’s out. You do not have to have smoke and explosions or stuntmen jumping out of windows.
Going through the checklists once a year is far better than once in five years organized spectacle; opting for both is ideal, of course.
What cybersecurity-related topics can be expected during the SG OGLF 2020?
“I’m sure that we cannot avoid talking about AI/ML,” said Savolainen. Topics on AI-powered-deep- fake-videos or netflow analysis will also be discussed.
Savolainen will also engage in discussing Cybersecurity as part of a foreign policy tool kit and on the international regulation of cyber weapons.
He looks forward to having an engaging session and delving into other topics, apart from these I hope there would be also something else than those hard-shelled things. “I would like to have a good conversation about smart city cyber issues from different angles,” he said.