|
Getting your Trinity Audio player ready...
|
Dr Matheus E Garbelini, a recent graduate from the Singapore University of Technology and Design (SUTD), has uncovered “high severity” security flaws within 5G chips, sounding the alarm for a potential global threat to mobile phones. Dr Garbelini, during his tenure as a PhD graduate student at SUTD, employed the Wireless Fuzzing technique to meticulously examine the firmware of 5G chips.
Collaborating with fellow PhD student Zewen Shang, Assistant Professor Sudipta Chattopadhyay, and researchers from the Agency for Science, Technology and Research’s Institute for Infocomm Research, the team unearthed critical findings that could have far-reaching consequences.
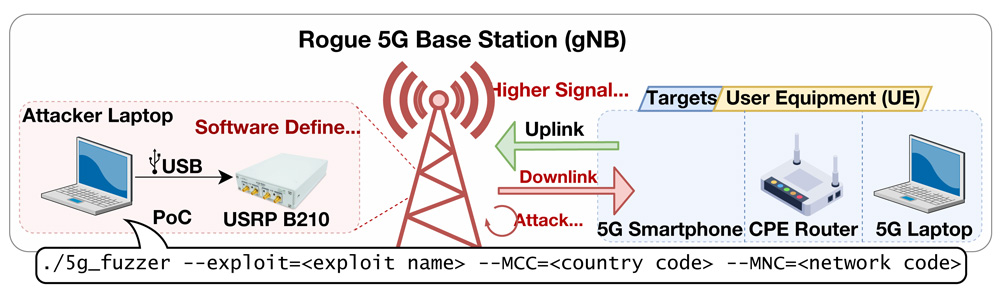
The vulnerabilities identified by Dr Matheus and his team reveal a significant “Denial of Service” (DoS) attack vector. In simpler terms, a malicious actor, armed with a rogue standalone 5G base station (gNodeB), could unleash an attack resulting in a complete loss of 5G connectivity for the targeted mobile phone.
What’s even more concerning is that the impact persists even after the attack concludes, with recovery necessitating a manual reboot of the affected device, often requiring the removal and reinsertion of the SIM card.
The gravity of these findings cannot be overstated, given the widespread usage of 5G chips in popular smartphone models worldwide. The SUTD team was commended for their contribution to identifying and addressing these security flaws.
Dr Matheus, who is currently a research fellow at SUTD, underscores the critical nature of these discoveries, particularly with the increasing adoption of 5G smartphones. The severity of the identified vulnerabilities lies in the lack of known defences against potential attacks.
However, Dr Matheus advises users to maintain the security of their devices by keeping their Android OS and iOS updated with the latest software patches, as these updates often include essential security enhancements.
Addressing security flaws in 5G chips is not just about fixing immediate issues but involves a comprehensive approach. Awareness of these flaws allows for proactive risk mitigation, enabling users, developers, and organisations to take preemptive measures such as implementing security patches and updates to reduce potential risks associated with vulnerabilities in 5G chips.
Preventing exploitation is a critical advantage of understanding and addressing these security flaws. By minimising the likelihood of malicious actors successfully exploiting vulnerabilities, the integrity and functionality of 5G networks, which transmit vast amounts of data, are safeguarded.
Data protection is paramount in the context of 5G networks, where security flaws could potentially expose sensitive information. Therefore, it is crucial to develop and implement robust encryption and security protocols to ensure the integrity and confidentiality of data.
Maintaining trust in 5G technology is fundamental for users and organisations relying on the security of these networks for various activities. Addressing security flaws, coupled with active measures to mitigate them, helps uphold trust in the technology and the entities providing it.
Compliance with industry standards and regulations is mandatory, especially in sectors handling sensitive data. Awareness of security flaws ensures organisations adhere to these standards and regulatory requirements, reducing legal and reputational risks.
Recognising security flaws fosters a culture of continuous improvement and innovation. Encouraging companies to enhance their products by addressing vulnerabilities makes them more resilient to emerging threats, contributing to the overall improvement of security across the entire ecosystem.
Awareness and action regarding security flaws are vital components in ensuring the robustness, reliability, and trustworthiness of 5G chips and the networks they support. The collaborative efforts of researchers like Dr Matheus and his team play a crucial role in uncovering vulnerabilities, prompting necessary measures to secure the future of mobile communication.